Massive WordPress Plugin Supply Chain Attack Uncovered
By Austin Ginder
AI Summary
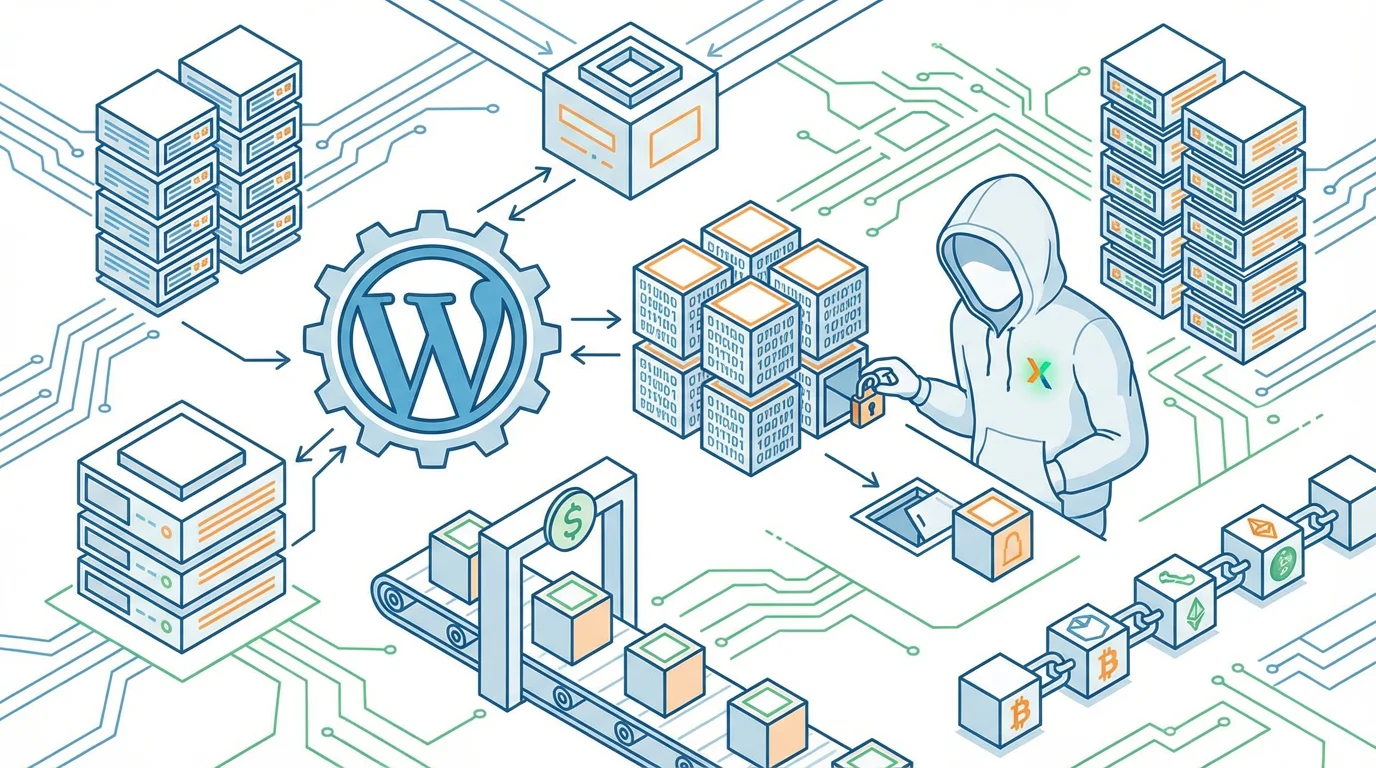
Recently, I uncovered a significant supply chain attack involving over 30 WordPress plugins, including the popular Countdown Timer Ultimate. These plugins, once trusted, were compromised after being acquired by a new owner, 'Kris', who has a background in SEO and online gambling. The plugins were sold on Flippa, and unbeknownst to many, a backdoor was planted, lying dormant for eight months before activation.
The attack involved sophisticated malware hidden in the wp-config.php file, which fetched spam links and redirects from a command-and-control server. This malware cleverly disguised itself, making it visible only to Googlebot and not to site owners. The attacker used an Ethereum smart contract to resolve the C2 domain, making traditional domain takedowns ineffective.
Despite WordPress.org's efforts to neutralize the threat by force-updating the plugins, the wp-config.php file remained compromised, continuing to serve hidden content. Through backup forensics, I pinpointed the exact moment of the injection, revealing a 6-hour window when the backdoor was activated.
The plugins' history showed that the malicious code was introduced in version 2.6.7, under the guise of a compatibility check. This version included a PHP deserialization backdoor, allowing arbitrary function calls controlled by a remote server. The plugins were originally developed by an India-based team and later sold when their revenue declined.
WordPress.org responded by permanently closing all 31 plugins from the Essential Plugin author in a single day. This incident mirrors a similar attack in 2017, where a buyer compromised multiple plugins for malicious purposes.
To mitigate the threat, I patched the affected plugins by removing the backdoor module and provided these patched versions for others to use. It's crucial for WordPress site managers to check their installations for these compromised plugins and take action to secure their sites.
This incident highlights a significant trust issue within the WordPress plugin marketplace, where ownership transfers can occur without adequate review or notification, leaving users vulnerable to such attacks.
Key Concepts
A supply chain attack involves compromising a trusted software or hardware provider to inject malicious code into products that are widely distributed to end users.
A backdoor is a method of bypassing normal authentication or encryption in a computer system, often used for malicious purposes to gain unauthorized access.
Category
SecurityOriginal source
https://anchor.host/someone-bought-30-wordpress-plugins-and-planted-a-backdoor-in-all-of-them/More on Discover
Summarized by Mente
Save any article, video, or tweet. AI summarizes it, finds connections, and creates your to-do list.
Start free, no credit card