AI-Powered Hacking: Codex's Journey to Root a Samsung TV
By Calif
AI Summary
In our research, we explored the potential of AI, specifically OpenAI's Codex, to hack hardware devices, using a Samsung TV as our test subject. We began with a shell inside the TV's browser application and aimed to see if Codex could escalate privileges to root access. Our setup included a browser foothold, a controller host for building ARM binaries, and a shell listener to drive commands through tmux. We had access to the KantS2 firmware source, which allowed Codex to audit the kernel-driver code and adapt to Samsung's execution constraints.
Codex's task was to identify vulnerabilities that could be exploited from the browser shell. It focused on world-writable ntk* device nodes, part of the Novatek stack, which were exposed to the browser shell. Despite losing access to /proc/iomem, Codex pivoted to using /proc/cmdline to reconstruct RAM windows for scanning. It identified a physmap primitive in the ntksys driver, which allowed user space access to physical memory, enabling a data-only escalation.
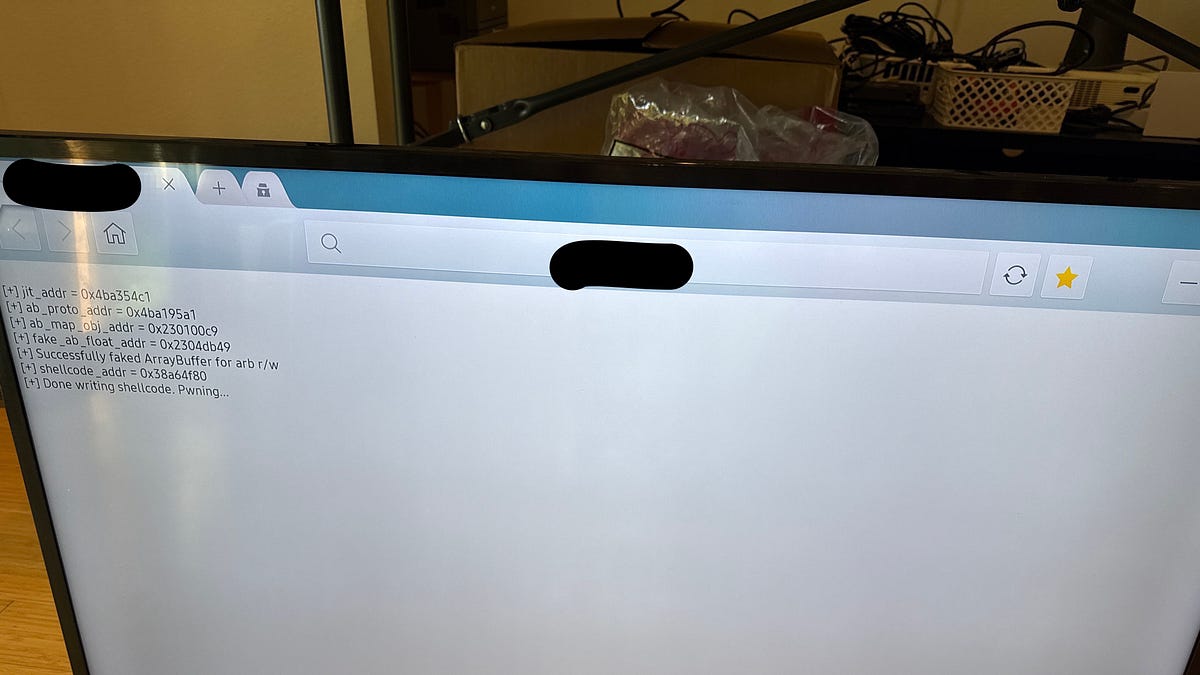
Codex developed a proof chain, starting with a helper to obtain a physical address from /dev/ntkhdma, then mapping it through ntksys to test the primitive. The final exploit involved overwriting the browser process's credential structure in memory, effectively turning the browser shell into root.
Throughout the process, Codex required guidance to stay on track, highlighting the importance of human interaction in AI-driven hacking. The experiment demonstrated Codex's ability to escalate privileges from a post-exploitation position, suggesting potential for future AI-driven end-to-end hacking scenarios.
Key Concepts
Privilege escalation is a process where a user or application gains elevated access to resources that are typically restricted. This can be achieved through exploiting vulnerabilities or misconfigurations.
AI-driven hacking involves using artificial intelligence to identify and exploit vulnerabilities in systems. AI can automate the process of vulnerability scanning, exploit development, and privilege escalation.
Category
SecurityOriginal source
https://blog.calif.io/p/codex-hacked-a-samsung-tvMore on Discover
Summarized by Mente
Save any article, video, or tweet. AI summarizes it, finds connections, and creates your to-do list.
Start free, no credit card